Expressvpn Glossary
Information security policy
What is an information security policy?
An information security (InfoSec) policy is a written set of rules that explains how an organization protects its information and the systems that store, process, or transmit it.
InfoSec policies commonly address the following areas:
- Security goals and scope: Data, devices, networks, and services covered.
- Ownership, accountability, and applicability: Who approves/maintains the policy, handles exceptions, and who must comply (employees, contractors, vendors).
- Data classification and handling: Sensitivity levels and protocols for labeling, storing, and transmitting information by its category.
- Required controls and behaviors: Rules on access, data handling, device use, and incident reporting.
- Risk and compliance alignment: How expectations tie to business risk and legal or contractual obligations.
How does an InfoSec policy work?
Implementation may differ depending on the organization, but some common methods are: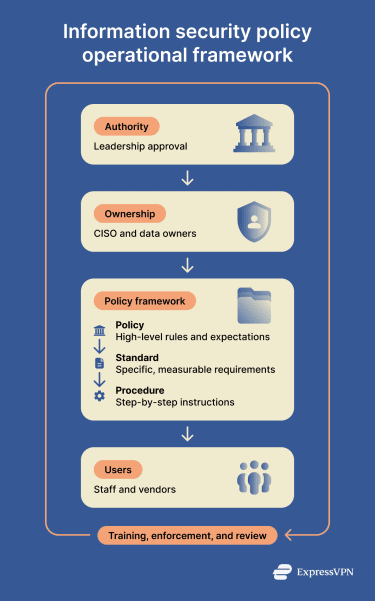
- Approval and authority: Leadership approval supports cross-departmental enforcement; security teams often draft it.
- Roles and responsibilities: A security leader, often a Chief Information Security Officer (CISO), typically owns the policy content and review cycle. System/data owners implement controls in their areas; staff and vendors comply according to their roles and contracts.
- From policy to action: Policy states the “what”; standards and procedures define the “how”:
-
- Policy: High-level rules and expectations.
- Standard: Specific, measurable requirements, such as password length or logging retention.
- Procedure: Step-by-step instructions, such as access requests or incident reporting steps.
- Training, enforcement, and review: Training supports a consistent understanding of policy requirements. Enforcement may include access reviews, monitoring, and audits. Reviews occur at regular intervals or after incidents, system changes, or risk shifts.
Where is it used?
InfoSec policies apply wherever sensitive data and connected systems exist, with examples varying by industry. Common areas include:
- Corporate information technology (IT) and Software-as-a-Service (SaaS) environments.
- Cloud services and hosted infrastructure.
- Remote work and bring-your-own-device (BYOD) programs.
- Regulated sectors (healthcare, finance, and government).
- Vendor onboarding, contract reviews, and third-party risk programs.
Why organizations create information security policies
Organizations create InfoSec policies to define expectations for protecting information and managing risk across systems and teams.
An InfoSec policy typically:
- Establishes shared rules for data handling and system access.
- Aligns security decisions with business risk and operational priorities.
- Defines roles, reporting paths, and responsibilities.
- Provides a reference point for audits, contracts, and regulator inquiries.
- Promotes consistent security practices across departments and vendors.
Further reading
- What is cybersecurity? A simple guide for beginners
- Security concerns in cloud computing and how to address them
- What is OPSEC, and why do you need it?


